Amazon Web Services Feed
Hardening code reviews on GitHub Enterprise repositories with Amazon CodeGuru
This post walks you through associating the GitHub Enterprise repository with Amazon CodeGuru Reviewer. This repository support is available for both self-hosted and cloud-hosted GitHub Enterprise options. In this post, we focus on associating CodeGuru with the repository on a self-hosted GitHub Enterprise Server.
CodeGuru Reviewer offers automated code reviews to catch difficult-to-find defects in the early stage of development. It is backed by machine learning models trained from millions of code reviews conducted within AWS and open-source projects. When the code repository is associated with CodeGuru, the creation of pull requests triggers CodeGuru to scan the code and, based on the analysis, provide you actionable recommendations. CodeGuru Reviewer currently identifies code quality issues in the following broad categories:
- AWS best practices
- Concurrency
- Resource leaks
- Sensitive information leaks
- Code efficiency
- Refactoring
- Input validation
In short, CodeGuru equips your development team with the tools to maintain a high bar of coding standards in the software development process. For more information about configuring CodeGuru for automated code reviews and performance optimization, see Automated code reviews and application profiling with Amazon CodeGuru.
In this post, we discuss the following:
- Support for GitHub Enterprise repositories: Cloud hosted and Self hosted
- Associating CodeGuru with GitHub Enterprise Server:
- Creating the repository provider association on CodeGuru
- Setting up the host (authorizing AWS CodeStar to access and install the app on an endpoint) and creating the connection (providing access to selected repositories)
- Completing the association of CodeGuru with the created connection
- Generating a pull request
- Cleaning up to avoid unnecessary charges
CodeGuru support for Cloud-hosted and self-hosted GitHub Enterprise repositories
GitHub Enterprise offers various ways to host repositories. When configuring CodeGuru to associate with GitHub Enterprise repositories, you can select GitHub for cloud hosted or GitHub Enterprise Server for self hosted. The cloud-hosted option refers to the GitHub cloud, whereas the self-hosted option refers to on-premises or the AWS Cloud.
For this post, we walk though configuring CodeGuru to associate with the self-hosted GitHub Enterprise Server.
We consider the following self-hosted options:
- With a public endpoint – The Amazon Elastic Compute Cloud (Amazon EC2) compute instance hosting GitHub Enterprise Server is accessible from the internet.
- With a private endpoint – This is a common scenario for an organization in which GitHub Enterprise Server is hosted on AWS Cloud as a private VPC endpoint and the developers securely access this endpoint from their corporate network or VPN. You could also host it on an on-premises server accessible via a specific VPC.
We revisit these scenarios later in this post when we configure the association with CodeGuru.
Before you associate GitHub Enterprise (GHE) repositories with CodeGuru, let us review our GHE server that is set up on our EC2 instance that will be hosting our repositories. The following screenshot shows the EC2 instance launched using the GitHub Enterprise AMI:
After you instantiate GitHub Enterprise Server on Amazon EC2 using the desired AMI, confirm its reachability by choosing its DNS name. If it’s configured with a private endpoint or an on-premises server, test the reachability using the endpoint URL from the appropriate source location and logging in.
Log in to the account and check your repositories. The following screenshot shows your repositories listed in the navigation pane.
In all these use cases, we recommend integrating Certificate Authority (CA) authorized certificates on GitHub Enterprise Server to enable a proper TLS handshake when accessing from a browser. If you’re using self-signed certificates on GitHub Enterprise Server, you may have to import those certificates in your browser to enable the TLS handshake and access the service.
Associating CodeGuru with GitHub Enterprise Server
This section summarizes the high-level steps to associate the self-hosted GitHub Enterprise Server code repository with CodeGuru Reviewer. To do so, we have to use the AWS CodeStar connections service, which offers a centralized place to create the association between a third-party service and an AWS service.
We first create an AWS CodeStar connection to GitHub Enterprise Server, then use this connection to list the repositories in that GitHub account and select the repository to associate with CodeGuru.
Creating the association
To start creating the association, complete the following steps:
- On the CodeGuru console, left pane, choose Reviewer.
- Choose Associated repositories.
- Select GitHub Enterprise Server.
- From the drop-down menu, check for any existing connections.
- If you don’t have any connections, choose Create a GitHub Enterprise Server connection.
The Create a connection window appears.
- For Connection name, enter a name.
- For Choose a host, choose the search box. If no hosts are configured, it displays an informational box.
- Choose Create host.
The host is configured to model the self-hosted GitHub Enterprise Server; for our use case, it’s hosted on our EC2 instance. This is configured only one time and later reused to create multiple connections in the same Region as the EC2 instance.
After you choose Create host, the Create host window appears.
- For Host name, enter a name.
- For Select a provider, choose GitHub Enterprise Server.
- For Endpoint, enter your endpoint.
- For VPC configuration, choose No VPC (we don’t need to configure a VPC for this use case).
The following screenshot shows an example of configuring for a self-hosted GitHub server that is accessible over the public internet.
For a GitHub Enterprise Server that isn’t accessible over the public internet, you need to choose Use a VPC and enter the following:
- VPC ID – The VPC ID where GitHub Enterprise Server is located or where the on-premises GitHub Enterprise Server is accessible from (a VPC with reachability to the on-premises GitHub Enterprise Server)
- Subnet ID – The subnets from the preceding VPC where GitHub Enterprise Server is located or where the on-premises GitHub Enterprise Server is accessible from
- Security group ID – The security groups that allow CodeGuru Reviewer to access GitHub Enterprise Server in the preceding VPC.
- TLS certificate – You don’t need to enter a TLS certificate if you’re using a certificate signed by a public CA on GitHub Enterprise Server. If you’re using a self-signed certificate or non-public certificate, enter the certificate. To obtain your certificate, complete the following:
- Navigate to your endpoint URL in Firefox.
- Choose the lock icon in the address field.
- Choose Connection, More Information.
- On the Security tab, choose View Certificate.
- On the Details tab, choose Export.
- Save it as a local file.
- Open the file in your preferred text editor to locate the certificate and copy and paste the text.
- Choose Create host.

You should now see the Setup status change from VPC configuration initializing to Pending.
- Choose Set up host.
Setting up the host and creating the connection
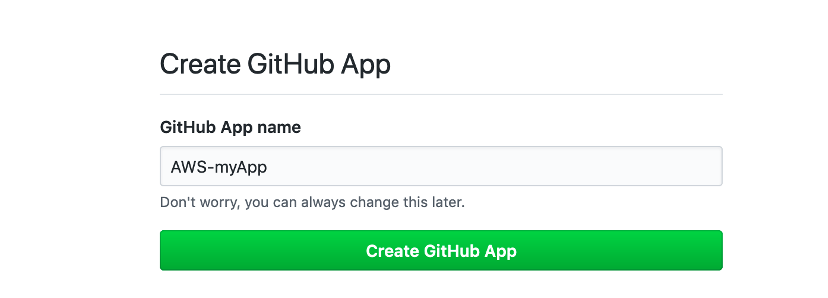
When you complete the steps in the previous section, you’re redirected to the Create GitHub App page. You need administrator login credentials for GitHub Enterprise Server to allow the application installation.
- After you log in with those credentials, for GitHub App name, enter a name.
- Choose Create GitHub App.
This step installs the app on GitHub Enterprise Server, and the host Setup status changes to Available.
- Choose Create connection. If the button isn’t available, complete the following:
- In the navigation pane, choose Settings.
- Choose Connections.
- Choose Create connection.
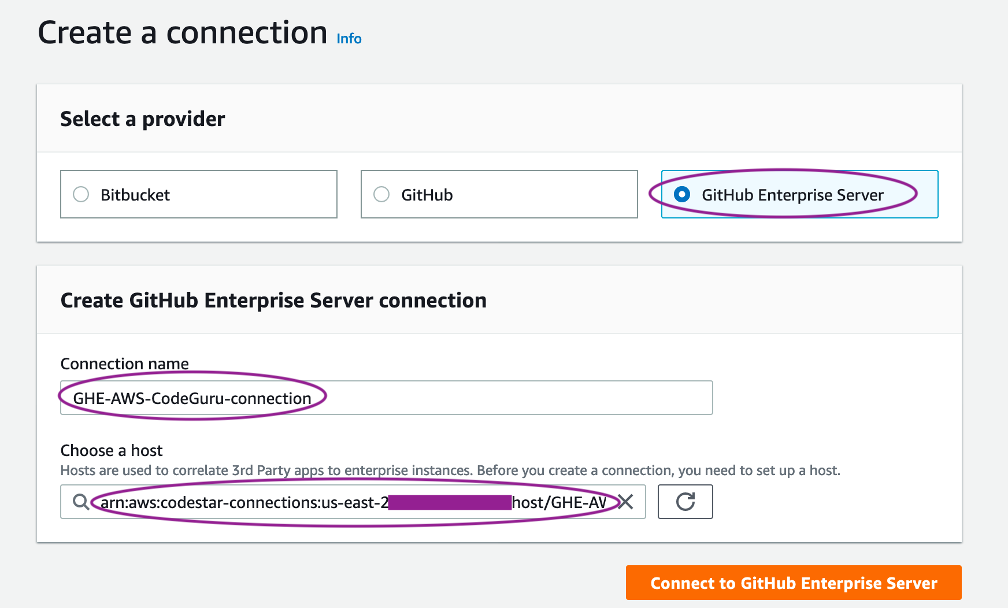
- On the Create a connection page, select GitHub Enterprise Server.
- For Connection name, enter a name.
- For Choose a host, enter your host.
- Choose Connect to GitHub Enterprise Server.
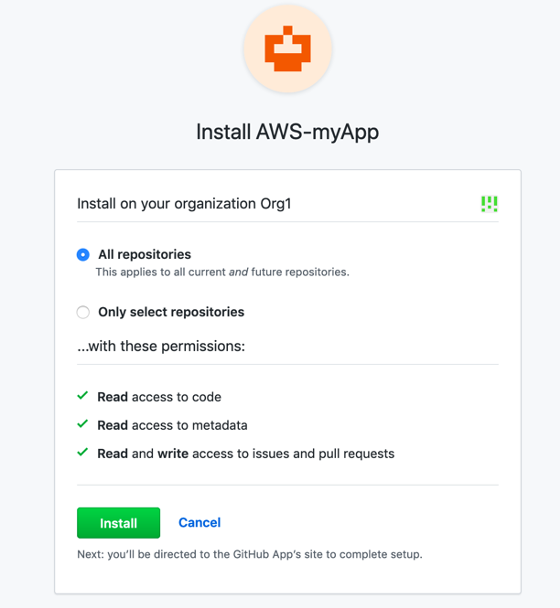
- In the window that appears, authorize the app installation.
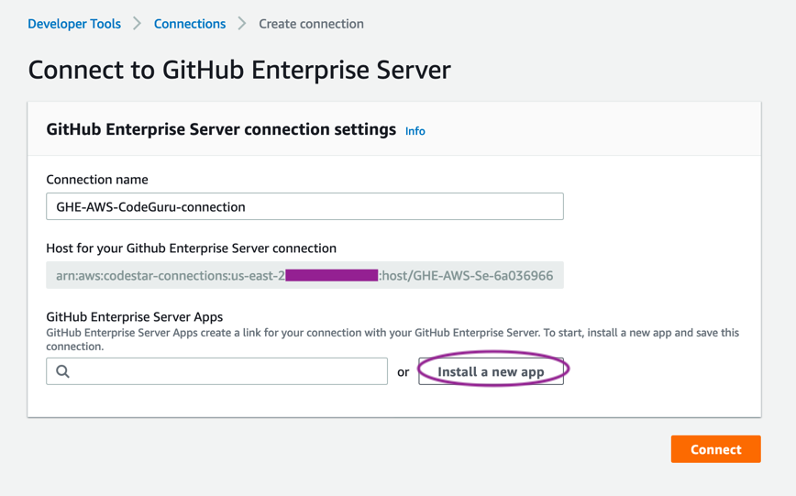
- On the Connect to GitHub Enterprise Server page, choose Install a new app.
- In the window that appears, select to apply All repositories or Only select repositories in that organization.
- When you return to the Connect to GitHub Enterprise Server page, choose Connect.
Completing the association of CodeGuru with the created connection
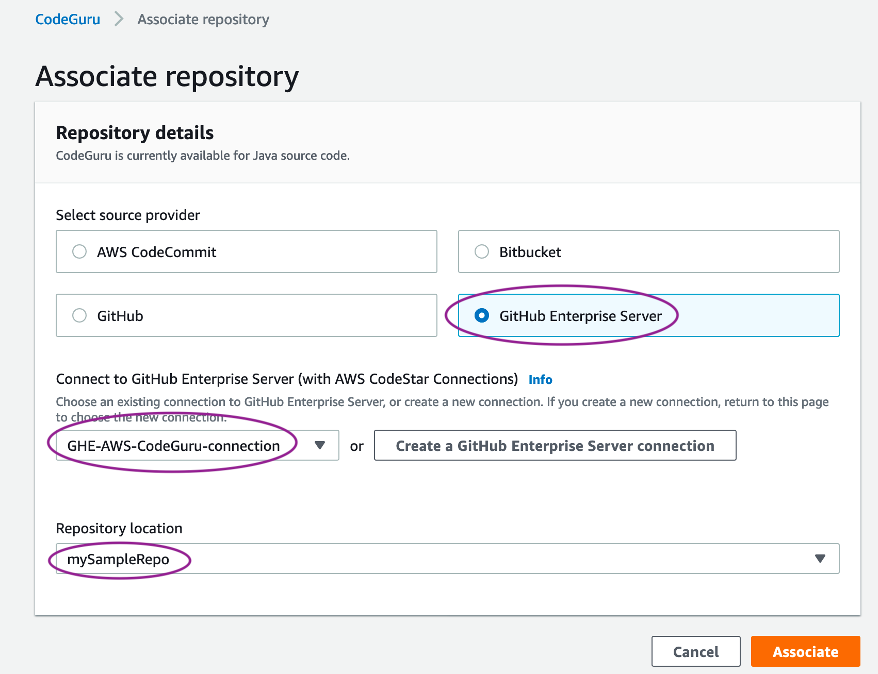
After you complete the steps in the preceding section, you return to the Associate repository page.
- For Select source provider, choose GitHub Enterprise Server.
- For Connect to GitHub Enterprise Server, choose your connection.
- For Repository location, choose your repository.
- Choose Associate.
In less than 30 seconds, the repository status shows as Associated.
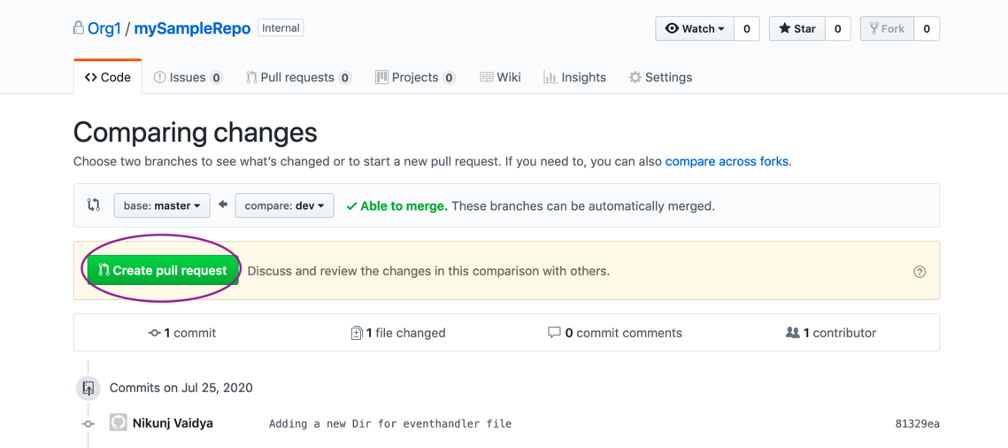
Generating a pull request
You’re now ready to create a pull request for any changes to the code and trigger CodeGuru to scan the code and generate actionable recommendations.
In your repository, on the Code tab, choose Create pull request.
You can see an active entry for the code review on the Code reviews page with the status Pending.
When it’s complete, you can see the recommendations on the Pull request tab.
Cleaning up
When you’re finished testing, you should un-provision the following resources to avoid incurring further charges:
- CodeGuru Reviewer – Remove the association of CodeGuru to the repository, so that any further pull request notifications don’t trigger CodeGuru to perform an automated code review
- GitHub Enterprise Server – If hosted on an EC2 instance, stop the instance
Conclusion
This post reviewed the support of self-hosted GitHub Enterprise Server repositories for CodeGuru Reviewer. You can take advantage of these features to enhance your application development workflow.
About the Author

Nikunj Vaidya is a Sr. Solutions Architect with Amazon Web Services, focusing in the area of DevOps services. He builds technical content for the field enablement and offers technical guidance to the customers on AWS DevOps solutions and services that would streamline the application development process, accelerate application delivery, and enable maintaining a high bar of software quality.